Responsible Cybersecurity practices include the process of helping our clients to mitigate their;
- Operational risks
- Litigation risks
- Reputational risks
With regards to data breaches that can occur to any entity on this planet due to poor software or hardware management practices.
ERI can help your organization;
- Develop and implement a Cybersecurity Framework
- Manage your risks and vulnerabilities. And we will protect all the data in your electronic hardware.
- Employ threat model and detection.
- Establish supply chain controls for all your hardware and electronics.
- Help develop, implement and test an Incident Response Plan.
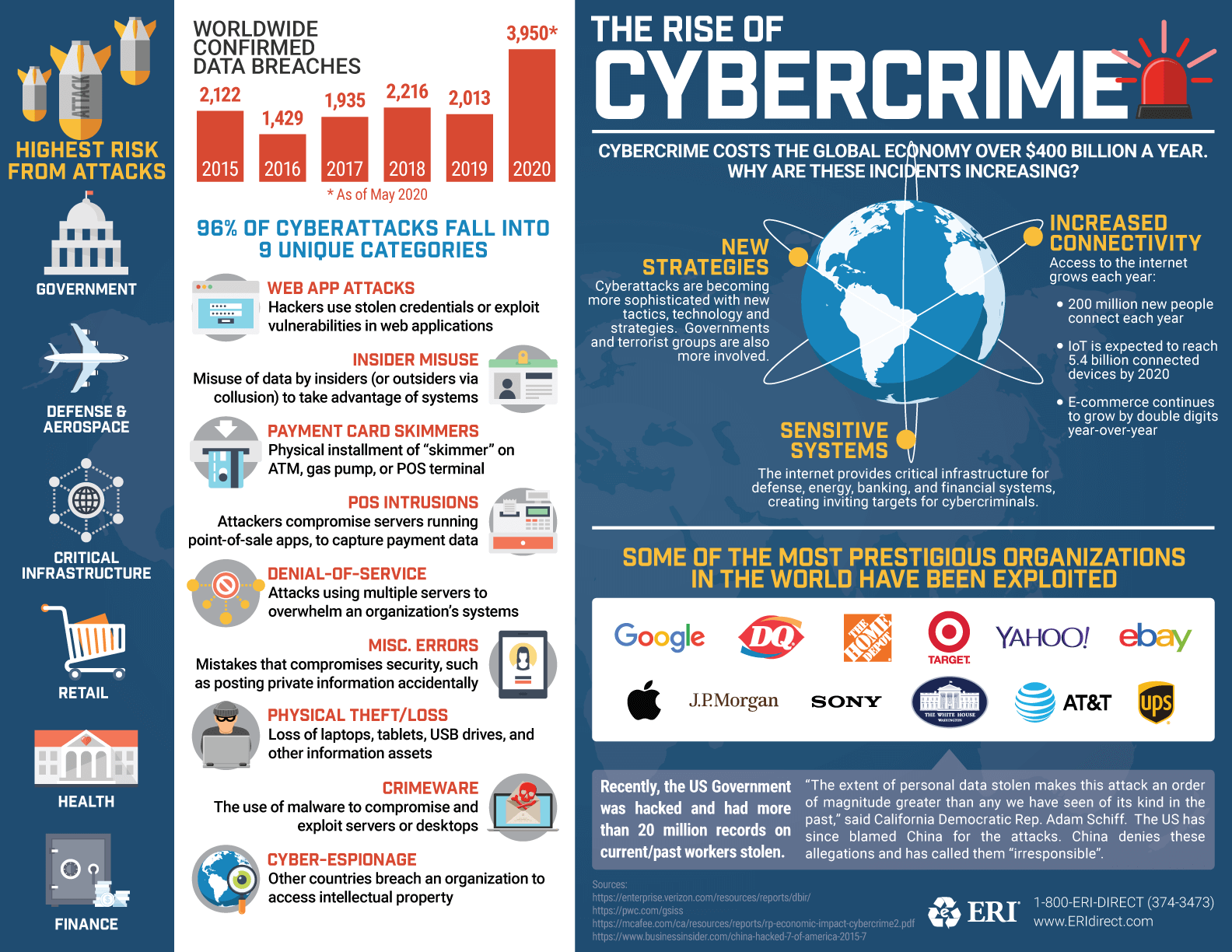
Learn More With Our “Rise Of Cybercrime” Infographic
Important Resources
-
Verizon Data Breach Investigations Report (DBIR)
Verizon
An annual publication that provides analysis of information security incidents, with a specific focus on data breaches.
-
Chief Information Security Officer (CISO) Workshop Training
Microsoft
Free training provided by Microsoft that includes a collection of security learnings, principles, and recommendations for modernizing security in your organization.
-
Hacker101
HackerOne
Hacker101 is a free class for web security. Whether you’re a programmer with an interest in bug bounties or a seasoned security professional, Hacker101 has something to teach you.
-
Data Breaches
ComplianceBoard
A community project where you can find information about data breaches, regulators and fines.
-
Cyber Security 101
PBS NOVA Labs
The Internet is fundamentally insecure. However, there are simple things you can do to protect yourself and your information. Learn what they are in NOVA’s Cyber Security Lab.
-
Cyber Security. Evolved.
Deloitte.
In less than 300 seconds, experience the speed and intensity of a cyber attack. As the plot unfolds, learn how companies can defend themselves, take control of the situation, and effectively fight back.
-
Cyber Security Overview
Homeland Security
Strengthening the security and resilience of cyberspace has become an important homeland security mission.
-
FACT SHEET: Cybersecurity National Action Plan
The White House
Cybersecurity Act of 2015: important tools necessary to strengthen the Nation’s cybersecurity, making it easier for private companies to share cyber threat information with each other and the Government.